Inside the British military base where young hackers learn to stop cybercrime | UK security and counter-terrorism | The Guardian

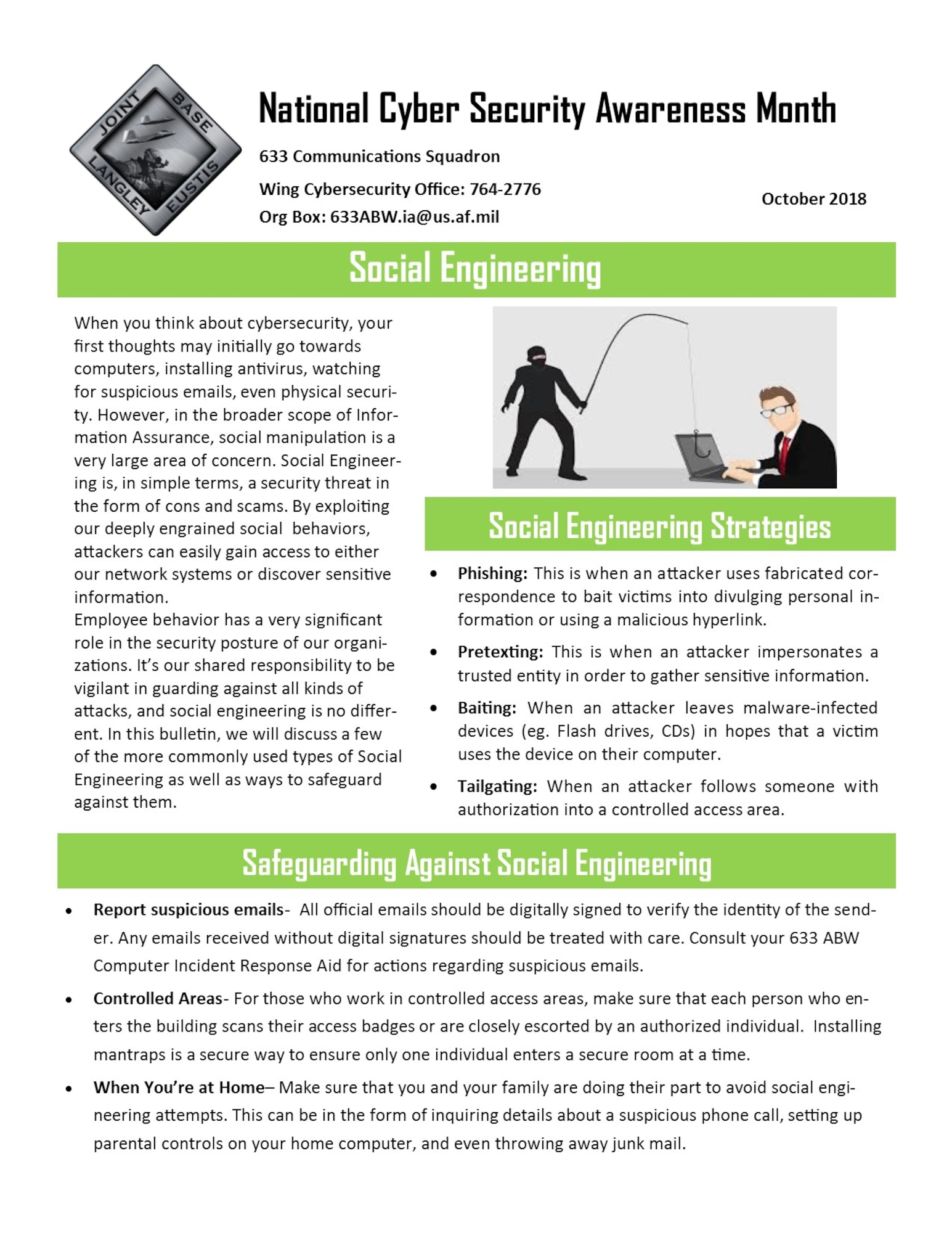
Building a base of cybersecurity experts in Indiana - WISH-TV | Indianapolis News | Indiana Weather | Indiana Traffic
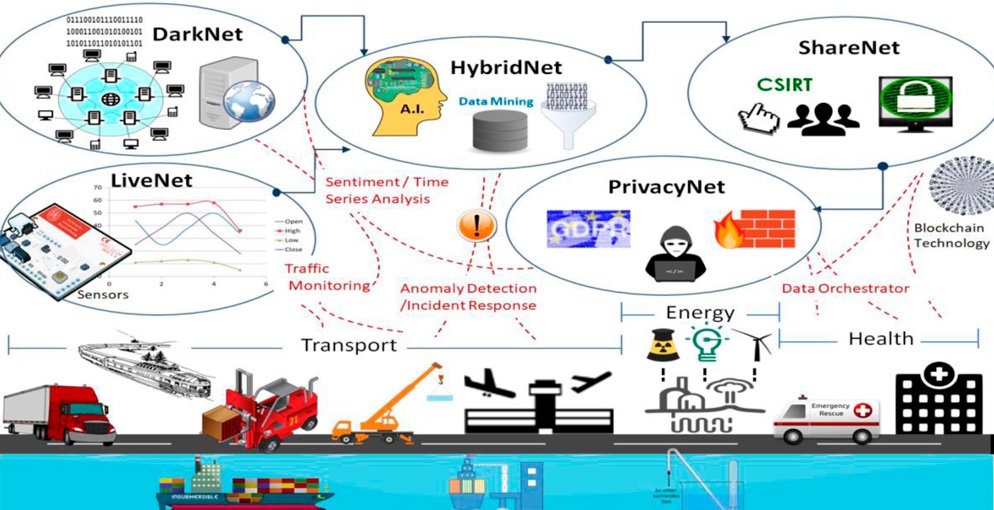
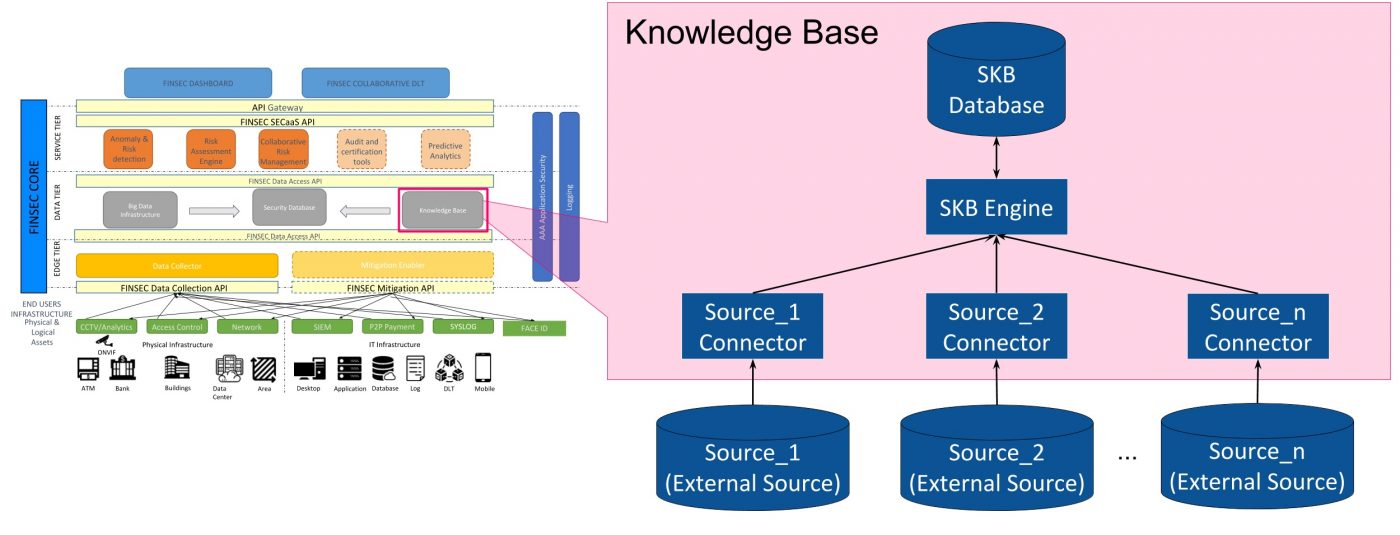
CYBERSANE - CYBER SECURITY INCIDENT HANDLING, WARNING AND RESPONSE SYSTEM FOR THE EUROPEAN CRITICAL INFRASTRUCTURES - Fundación Valenciaport